Filter by Topic
Filter by Vendor
Certified Ethical Hacker | CEH eLearning
Course Description The Certified Ethical Hacker (CEH) provides an in-depth …
What you'll learn
Information security controls, laws, and standards.
Various types of footprinting, footprinting tools, and countermeasures.
Network scanning techniques and scanning countermeasures
Enumeration techniques and enumeration countermeasures
Vulnerability analysis to identify security loopholes in the target organization’s network, communication infrastructure, and end systems.
System hacking methodology, steganography, steganalysis attacks, and covering tracks to discover system and network vulnerabilities.
Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures.
Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing.
Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures.
DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures.
Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures.
Webserver attacks and a comprehensive attack methodology to audit vulnerabilities in webserver infrastructure, and countermeasures.
Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures.
SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures.
Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools.
Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools.
Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures.
Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools.
Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap.
Threats to IoT and OT platforms and defending IoT and OT devices.
Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools.
VMware vSphere: Skills for Operators 6.7
Course Description This two-day training course is for operators and …
What you'll learn
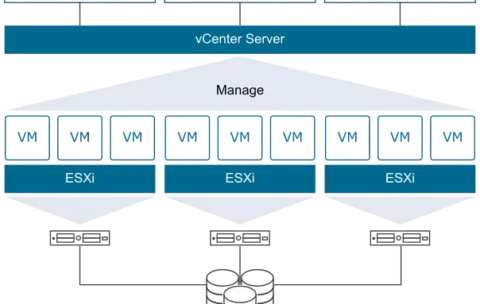
Describe virtualization, virtual machines, and vSphere components
Describe the concepts of server, network, storage, and desktop virtualization
Deploy, configure, clone, and manage virtual machines
Use VMware vCenter Server® to monitor virtual machine resource usage
Use VMware vSphere®vMotion® and VMware vSphere® Storage vMotion®to migrate virtual machines
Use VMware vSphere® Distributed Resource Scheduler™ and VMware vSphere® High Availability to optimize the performance of your vSphere virtual environment
VMware vSphere: Optimize and Scale plus Troubleshooting Fast Track 7.0
Course Description This accelerated, hands-on training course is a blend …
What you'll learn
Introduce troubleshooting principles and procedures
Use command-line interfaces, log files, and VMware vSphere® Client™ to diagnose and resolve problems in the vSphere environment
Describe the benefits and capabilities of VMware Skyline
Explain the purpose of key vSphere log files
Monitor and analyze key performance indicators for compute, storage, and networking resources for
VMware ESXi™ hosts
Optimize the performance in the vSphere environment, including VMware vCenter Server®
Identify networking problems based on reported symptoms, validate, and troubleshoot the reported
problem, identify the root cause, and implement the appropriate resolution
Analyze storage failure scenarios using a logical troubleshooting methodology, identify the root cause, and apply the appropriate resolution to resolve the problem
Troubleshoot vSphere cluster failure scenarios and analyze possible causes
Diagnose common VMware vSphere® High Availability problems and provide solutions
Identify and validate ESXi host and vCenter Server problems, analyze failure scenarios, and select the correct resolution
Troubleshoot virtual machine problems, including migration problems, snapshot problems, and connection problems
Troubleshoot performance problems with vSphere components
VMware NSX: Install, Configure, Manage plus Troubleshooting and Operations Fast Track 6.4
Course Description This intensive five-day, extended-hours course focuses on installing, …
What you'll learn
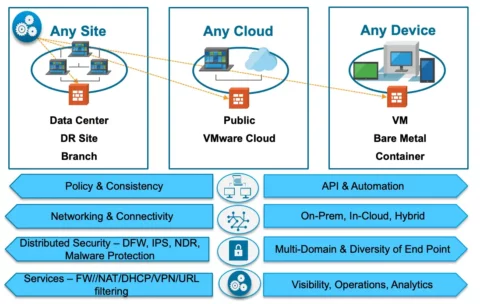
Describe the evolution of the software-defined data center
Configure and deploy VMware NSX components for management and control
Describe basic VMware NSX layer 2 networking
Configure, deploy, and use logical switch networks
Configure and deploy VMware NSX distributed router appliances to establish east-west connectivity
Configure and use all main features of the VMware NSX® EdgeTM services gateway
Configure NSX Edge firewall rules to restrict network traffic
Configure VMware NSX distributed firewall rules to restrict network traffic
Configure Service Composer policies
Configure an identity-aware firewall
Describe VMware NSX data security
Use the cross-vCenter VMware NSX feature
Establish and apply a structured approach and methodology for troubleshooting
Troubleshoot NSX infrastructure and component problems
Troubleshoot physical and logical networking problems involving switching and routing
Use tools to monitor, operate, and troubleshoot NSX deployments
VMware NSX: Install, Configure, Manage 6.4
Course Description This five-day, comprehensive, fast-paced training course presents VMware …
What you'll learn
Configure and deploy NSX components for management and control
Describe basic NSX layer 2 networking
Configure, deploy, and use logical switch networks
Configure and deploy NSX distributed router appliances to establish east-west connectivity
Configure and deploy VMware NSX® Edge™ services gateway appliances to establish north-south connectivity
Configure NSX L2 bridging
Configure and use all main features of the NSX Edge services gateway
Configure NSX Edge firewall rules to restrict network traffic
Configure NSX distributed firewall rules to restrict network traffic
Configure Service Composer policies
Configure an identity-aware firewall
Describe NSX data security
Use the cross-vCenter NSX feature
AWS Certification Exam Readiness Workshop: AWS Certified Solutions Architect – Professional
AWS Certification Exam Readiness Workshop By CCS Learning Academy gives …
What you'll learn
Content domains and how AWS services map to them
Combine multiple AWS services to solve complex architectural requirements
Advanced concepts of core AWS services and associated use cases
Identify how questions are written to test AWS architectural concepts
PeopleCert Scrum Developer
Course Description The PeopleCert Scrum Developer certification covers the fundamental …
PeopleCert Scrum Product Owner II
Course Description The PeopleCert Scrum Product Owner II certification covers …